By Lukas Aichbauer | March 08, 2024 | 9 min read
How Do You Choose A Docker Base Image?
Size, security, and compatibility are the basis for choosing your ideal Docker image for your application. With this article, you will learn how to select the right base image while keeping an eye on the previously mentioned aspects.
Table of Contents
- What Is a Docker Base Image?
- What Are Some Best Practices for Selecting and Maintaining Docker Base Images?
- How Does Size Influence The Choice Of A Docker Base Image?
- Why Is Security a Crucial Factor in Choosing a Docker Base Image?
- What Are Some Common Docker Base Images and Their Advantages?
- What is FROM scratch In Docker and when to use it?
- Conclusion
What Is a Docker Base Image?
A Docker base image is the starting point for building any Docker image. Yes, that sounds confusing. You are probably asking yourself: “Why do you need a Docker image to build a Docker image? Is this the chicken or the egg problem?”. Well, yes and no. You can imagine it like this. There are two ways to create a Docker image. From scratch or based on an already built image. When you build your Docker image, consider it your canvas; you can either start with a blank one or paint on a pre-designed one. To make it even more confusing, you will hear the term parent image when you are talking about using an already built image. Officially by Docker, only images starting with FROM scratch are called base images. Images that start from another image are called parent images. However, the terms are used interchangeably by the community, and most developers talk about base images most of the time. Knowing that, we will use base image as the broad term for our starting images.
What Are Some Best Practices for Selecting and Maintaining Docker Base Images?
- Assess Your Needs: Understand the requirements for your application in terms of size, performance, and compatibility.
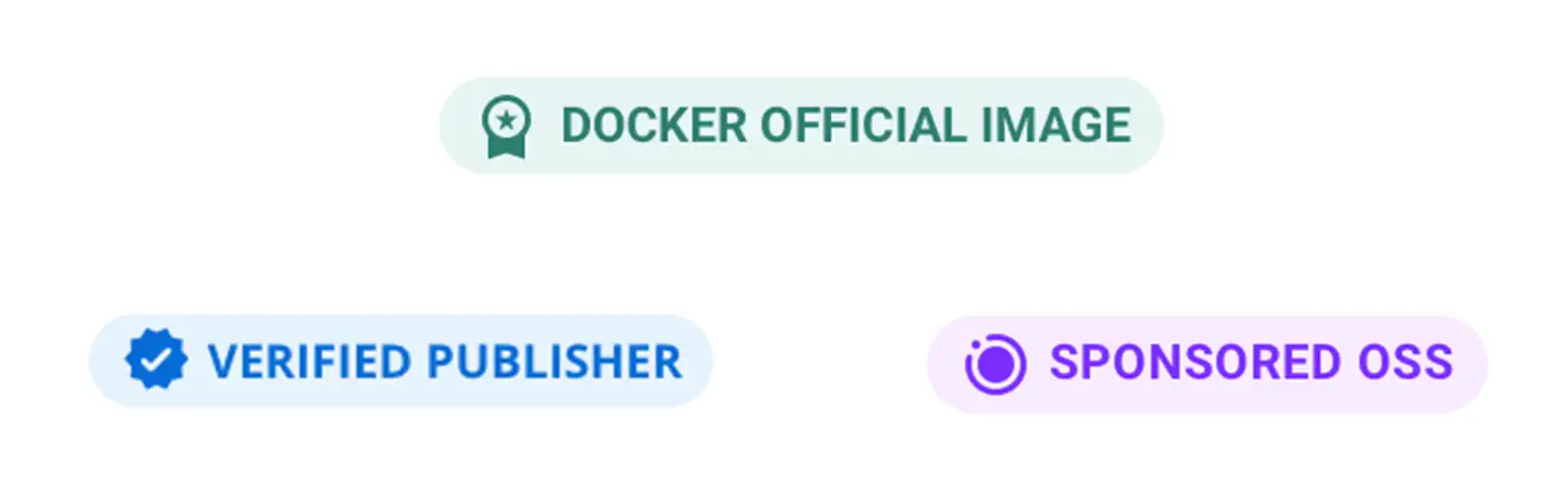
- Prioritize Security: Choose images from trusted, reputable sources and ensure regular updates. In Docker Hub, look at the Docker Official Image badge.
- Keep It Minimal: Opt for base images that include only what you need to reduce size and security risks. Use Alpine based images or scratch when you have a single binary. Images with a postfix slim indicate that this image is minimal.
- Regularly Update and Patch: Use Tools to continuously monitor and update your base images to patch vulnerabilities.
- Test Compatibility: Regularly test your application against the latest version of your base image to ensure compatibility. Do not use latest by default. This could mean that your application stops working one day, as a new version of the image could break something in your application. Fix it to a version and regularly update the version of your image.
- Customize Only When Necessary: Do not reinvent the wheel. Most of the time, an existing image can be used. But sometimes, it is necessary to create a custom base image tailored to your application’s specific needs.
How Does Size Influence The Choice Of A Docker Base Image?
The size of a Docker base image plays a significant role in your application’s performance and deployment speed. Larger images like Ubuntu take longer to download and consume more storage, which can be a concern in environments where resources are limited or costs are high. Conversely, smaller images, like Alpine Linux, are lightweight and faster to deploy, making them ideal for applications that require rapid scaling or deployment.
- Download Time: The larger the size, the longer it takes to download the image, especially in environments with slower internet connections or bandwidth limitations. Take that into account for your CI/CD pipeline as well.
- Storage Space: Larger images consume more storage space on a disk. This can be important when disk capacity is limited (e.g., deploying on an IoT device like a drone, a satellite or a smart fridge) or in cloud environments where disk space impacts cost.
- Start-up Time: Smaller image sizes lead to faster startup times for containers, enhancing the efficiency of the deployment process.
Why Is Security a Crucial Factor in Choosing a Docker Base Image?
The Docker base image is the foundation of your application and sets the standards for your applications’ security. To make an informed decision about a Docker image, you need to consider various factors.
- Foundation: If the base image is not “secure”, your application placed in that environment will not be secure as well.
- Vulnerability Reduction: Every Docker image can contain a vulnerability. To reduce the chance for a security vulnerability, we should choose a Docker image that is regularly updated with security patches. If your image was not updated for a long time, you should not use it.
- Attack Surface Minimization: If your base image has unused packages in it, this will increase the attack surface. You need to update and keep track of packages that you are not even using. That’s why selecting smaller Base images can be more secure.
- Compliance: In many industries, applications need to comply with specific security standards and regulations. You may have to create your own Docker base image that fits your specific needs.
- Reputation and Trust: Make sure you use trustworthy sources for your images. In Docker Hub, you can identify them with the Docker Official Image badge. Trusted sources maintain their images with a focus on security, regularly scanning for vulnerabilities and issuing timely updates and patches. https://docs.docker.com/trusted-content/
- Compatibility: If you have a Node.js application, you should use Docker images that are compatible with this programming language. If you are using a python image for your Node.js application, you would just increase the attack surface, as it has packages and libraries installed that you do not need for running your application.
What Are Some Common Docker Base Images and Their Advantages?
- Alpine: Known for its minimal size and security features. Ideal for lightweight, security-focused applications.
- Ubuntu: Offers a balance between functionality and size. It’s widely used due to its extensive package repositories and support.
- Node, Golang, Python, …: There are a ton of official images that are designed for a specific programming language. If you develop a Node.js application, consider using the official node image. They often offer minimal solutions like Node Alpine, Python Slim, or Golang Alpine.
- Postgres, RabbitMQ, Redis, …: Many open-source applications, like databases, in-memory databases, and messaging brokers offer official images. You can use them if you need that functionality. Consider those images before configuring your images for your databases, messaging brokers, or other custom applications.
- Scratch: The most minimal base image, used to create the smallest possible container. This image is empty. Best for highly specialized, minimalistic applications. If you have a single binary that already includes all dependencies, you can choose this Docker image. This image is also used to create general base images like, Alpine, Ubuntu, and many more.
What is FROM scratch In Docker and When To Use It?
Only if you have a binary containing all its dependencies or no existing image fits your need, you should opt for the scratch image and start creating your own. You would have to manage everything, from the operating system, file system, packages, and so on yourself. Most base images start with FROM scratch like the official Alpine, Debian, or Busybox images. Images like NGINX utilize those base images. For example, the official NGINX image uses the Debian image as foundation for its image. And you could use the NGINX image as a base for your web application. Therefore, you could say, it is an “all roads lead to scratch” situation.
Do I Need To Use The Scratch Base Image?
Most of the time, when we are building an application, we just want to place our application somewhere so it will run reliably. In most cases, we would not start FROM scratch. There are exceptions, for example, if you have a binary that does not rely on any system packages. It would be a smart move to use FROM scratch as this is the smallest possible image size that you can get, and also the most secure.
Conclusion
In conclusion, selecting the right Docker base image is crucial for the overall performance, security, and compatibility of your application. It is a decision that goes beyond technicalities, impacting the strategic foundation of your project. This choice should be made with a clear understanding of the specific requirements for your application and the operational environment. Opt for a base image that is lightweight, secure, and regularly updated to ensure your Dockerized application remains robust, efficient, and secure throughout its lifecycle.
If you need help with your containerization, feel free to contact us, or join our new community for further questions and discussions!
You liked this article? Share it with your colleagues and friends.
Sign Up For Our Newsletter
Do not miss out on our latest tips, guides, and updates – sign up for our newsletter now! We promise to only send you the most relevant and useful information. Be part of our journey in exploring the world of Docker and beyond.